BMS Cybersecurity Products and Solutions
By default, the Eclypse and EC-Net are secure platforms when placed in an appropriate network environment and setup by following the appropriate user guide. We recommend to always run the latest firmware available from the software center and never place the controller directly on a public network.
Eclypse
Eclypse Connected Controller platform for future-ready buildings providing comfort management, efficiency, and unrivalled, proven connectivity open to digital services.
Physical Security
Protection of the physical assets that are hosting the data we wish to secure.

Secure Boot
Eclypse APEX only. Benefit from secure boot and cybersecure communication between OT, IT, and cloud-based platforms, making it the ideal all-in-one solution for local and remote applications.Network & System Security
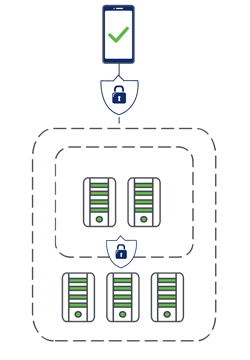
A network perimeter demarcates the boundary between an organization’s intranet and the external or public-facing internet. Vulnerabilities create the risk that attackers can use the internet to attack resources connected to it.3

3https://www.gartner.com/en/topics/cybersecurity
Authentication
- Single Sign-On (SSO) with ECY-APEX as an Identity Provider
- Eclypse Authentication is Basic or SSO, using OpenID Connect.
- The SSO service allows a user to use one set of login credentials (e.g. username and password) to access multiple Eclypse controllers that are on the same network. This provides a secure centralized login method to authenticate users.
- The basic functionality behind an SSO service with Eclypse controllers is the Client-Server architecture where one controller is defined as the Server dedicated to authentication/authorization purposes to access the Client controllers.
- The SSO authenticates the user for all the controllers the user has been given rights to and eliminates further login prompts when the user accesses other controllers within the same session.
- The session ends if you close the web browser or you log out. It is recommended that you close your web browser after logging out.
Secured-by-Design
- Compliant with Secured-by-Design standards, this end-to-end security system ensures the highest levels of cybersecurity, meeting frameworks like Zero Trust Security, NIST Cybersecurity Framework (NIST SP 800 82), and Cybersecurity of Facility-Related Control Systems (UFC 4-10-06).
User Authorization
- RBAC (Role-Based Access Control)
General Security Requirements
- All Security Requirements for Eclypse derived from ISA 62443 Security Level 4
Access Control
Identity infrastructure and PKI integration- PKI
- SSO
Topology
- RESTful API
Data Security
It comprises the processes and associated tools that protect sensitive information assets, either in transit or at rest. Data security methods include encryption, which ensures sensitive data is erased, and creating data backups.4
4https://www.gartner.com/en/topics/cybersecurity
Encryption
Data Encryption
- Eclypse Controllers have encryption that meets the FIPS 140-2 federal standard except for ECY-STAT and APEX.
- Basic security audit logs containing information about changes to the users as well as user successful and unsuccessful sign-ins.
- Meets encryption standards for mission-critical industries such as banking and for US government contracts.
Standards and protocols
- TLS minimum Protocol Version: TLSv1+, TLSv1.1+, or TLSv1.2
Digital signatures
- SHA256withRSA (2048-bit RSA asymmetric key)
Application Security
The tools available to monitor and confirm the state of the system’s security posture.

Monitoring
Security Audit Log
- Basic security audit logs containing information about changes to the users as well as user successful and unsuccessful sign-ins.
It is the responsibility of the developer to account for the intellectual property and security concerns when they are building and programming a docker compatible image. Additionally, use the best practices when deploying the docker container over IoT Edge. See Microsoft and Docker documentation for more details and best practices
Cybersecurity Best Practice Websites
EC-Net
The EC-Net™ web-based building management platform is powered by the Niagara Framework® to provide all the essential functionality required for single buildings up to large, multi-site deployments. EC-Net was developed with an approach to cybersecurity that can be customized to the security policy of any organization. The approach for doing this revolves around making it easier for users to secure an EC-Net system, along with enforcing good “cyber behaviour” through technology controls.
Physical Security
Protection of the physical assets that are hosting the data we wish to secure.

Secure Boot
EC-BOS will only boot-up with digitally signed trusted software, providing assurance against alterationNetwork & System Security
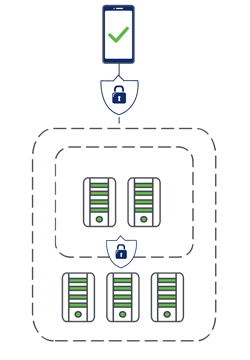
A network perimeter demarcates the boundary between an organization’s intranet and the external or public-facing internet. Vulnerabilities create the risk that attackers can use the internet to attack resources connected to it.1

1https://www.gartner.com/en/topics/cybersecurity
Authentication
“Secure by Default”
- Users forced to have strong password strengths
- Users set up with the strongest authentication mechanism
- User lockouts upon consecutive bad log-ins
- Factory default password must be changed after commissioning
Single Sign-On with EC-Net as an Identity Provider
- SSO allows users to login into one station and access all other connected stations via a browser without having to re-authenticate.
- Eliminates need to manually configure and manage an external IdP.
Multi-Factor Authentication (MFA)
- Google 2 Factor Authentication
Digital certificate authentication
- Beneficial for kiosks via browser web connections
802.1x device network authentication
Access Control
Identity infrastructure and PKI integration
- LDAP
- Kerberos
- SAML 2 Identity Providers for Single Sign-On
Role-Based Access Control
- Provides access control for users by security role
- Managed by CategoryService and RoleService and assigned within UserService
Authorization
Authorization at API level
- Controls what individual software components can do
Standard and protocols
- SCRAM-SHA (256/512 bit) DIGEST – default
- EC-BOS-8: WPA-PSK128, WPA2PSK256
- Google 2 Factor Auth
- Client Cert Auth (Kiosk Mode)
- PKI
- LDAP
- Kerberos
- SAML 2 IDP SSO Integration
Data Security
It comprises the processes and associated tools that protect sensitive information assets, either in transit or at rest. Data security methods include encryption, which ensures sensitive data is erased, and creating data backups.2
2https://www.gartner.com/en/topics/cybersecurity
Encryption
Data Encryption
- All connections to stations are secured and encrypted, e.g. workbench to station, station to station and web connections
- Both EC-BOS and EC-Net Supervisor have encryption that meets the FIPS 140-2 federal standard.
- Meets encryption standards for mission-critical industries such as banking and for US government contracts.
- Data is encrypted when sent/received, as well as at rest
Encrypted Protocols
- BACnet Secure Connect
Built in PKI management tools
- Niagara can integrate with any PKI infrastructure, LDAP directories, Kerberos
Third-Party Module Signing
- EC-Net now enforces the signing of newly added modules and makes administrators aware of any existing, unsigned third-party modules.
- Automatically eliminates the risk that modules may have been tampered with or come from an untrustworthy source.
Standard and protocols
- TLS 1.3, 1.2, 1.1, 1.0 issued with RSA 2048 bit certificate, SHA256withRSA
- AES 256-CBC Symmetric Key Encryption
- AES GCM)
- PBKDF2-HMAC-SHA256
- Digital signatures: SHA256withRSA (2048-bit RSA asymmetric key)
- FIPS 140-2 cryptographic module
Application Security
The tools available to monitor and confirm the state of the system’s security posture.

Monitoring
Security Audit Log
- Provides users with a history of who, or what, is logging into or changing security-related settings on an EC-Net station
Security Dashboard
- Provides an actional view into security posture of your systems & other connected Niagara systems on your network





